In order to protect your Docker images, it’s important to understand some basics of how Docker image vulnerability assessment work. Here are some tips that will help you better manage your containers so they’re not easily hijacked by malicious actors.
We should know the basics of container vulnerabilities. Some of the most common vulnerabilities in containers include unpatched packages and misconfigurations that could lead to privilege escalation, among others. It’s also worth knowing the difference between accidental software flaws (i.e., bugs) and intentional ones (i.e., malware). This gives us a clearer understanding of what you might be dealing with when it comes to defending from hacks like these.
We should also know how to patch containers. If you’re hosting and managing your own Docker containers, then it’s important that you install updates as soon as they’re released. If you use tools like Docker Cloud, then your images are automatically updated on a regular schedule according to the policies that you set up. But if you host your own images via the open-source Docker engine, it’s up to you to decide how often they get patched.
It is important to understand that Docker image assessment is very important for security aspects. We must understand what image assessment tools can do for us. Vulnerability assessment tools are used to see what’s vulnerable in our Docker images. The best resources we have found for this are Docker’s official documentation of their scanning tools and their guide to vulnerability assessment.
In this blog, we will perform Docker’s image vulnerability assessment using Clair Scanner.
Read More: Introduction to Docker and How Docker can be used as Pentesting?
What is Clair Tool?
Clair scanning tool is a prerequisite for docker’s image vulnerability scanning and assessment. It is an open-source tool for the analysis of vulnerabilities in docker containers.
How to perform Vulnerability Assessment of Docker Image using Clair Tool?
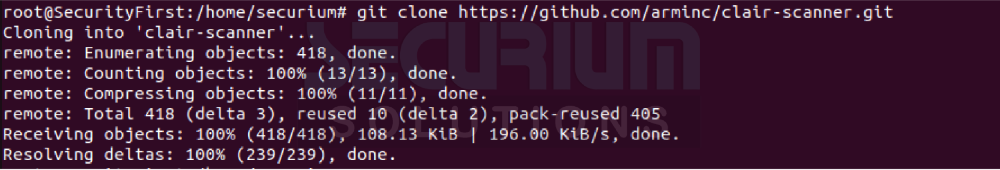
We will use the following command to clone the Clair tool package:
# git clone https://github.com/arminc/clair-scanner.git
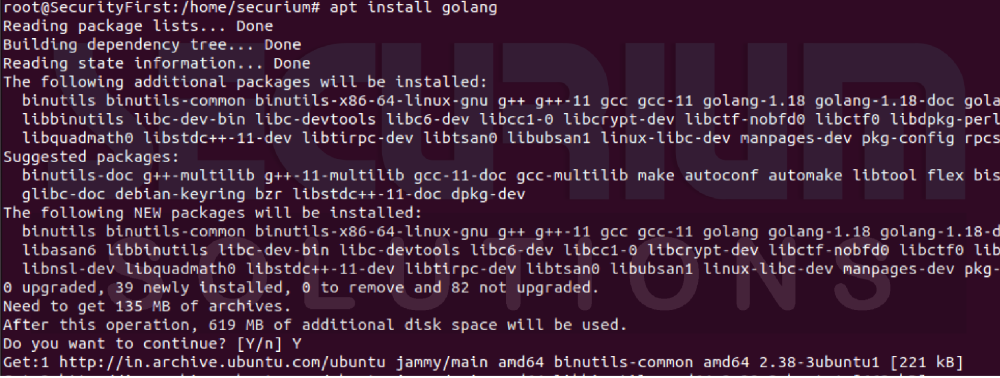
Clair scanner is developed in go language. So, we have to install the golang in our local machine. To install golang, run the given command:
# apt install golang
After installing golang, we have to install make command in order to build the library using the given command:
# apt install make
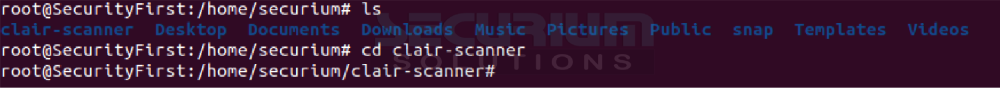
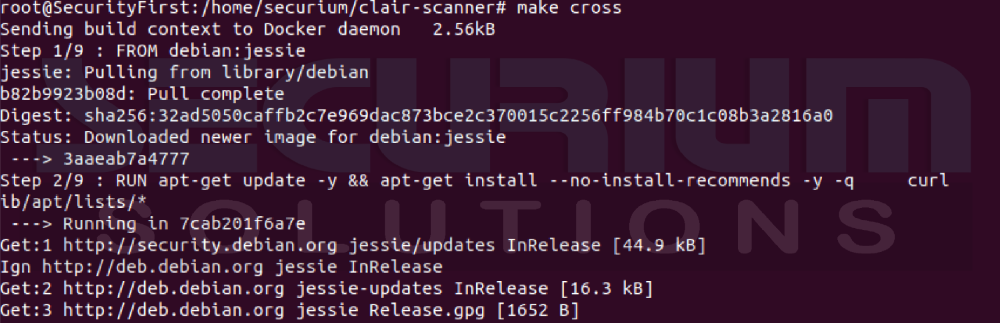
Now we will build the library using make command which is mandatory to install all the dependencies of the Clair scanning tool. For that, run the following commands:
# ls
# cd clair-scanner/
# make build
# make cross
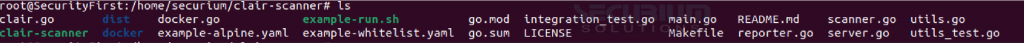
After pulling the library, we can see the clair-scanner file using ls command:
# ls
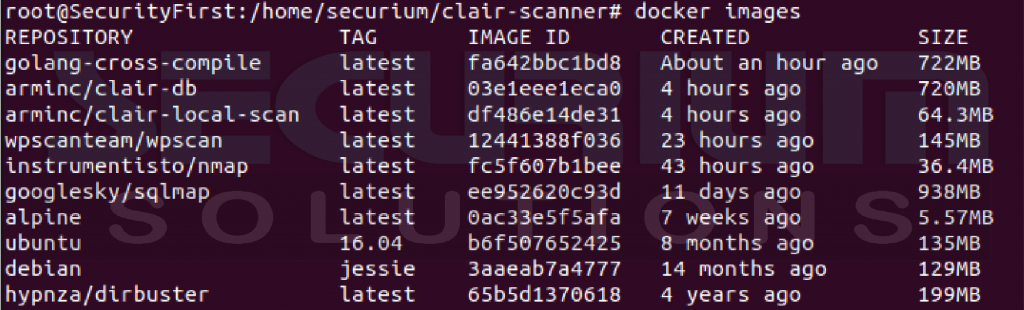
Now we will check whether we have any docker images or not by the following command:
# docker images
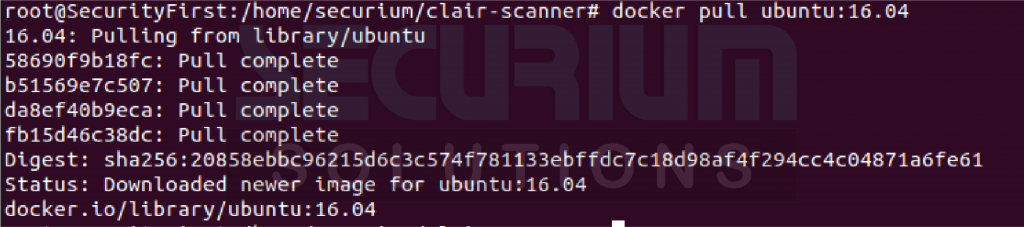
We can also pull an Ubuntu image for vulnerability scanning and assessment using the given command:
# docker pull ubuntu:16.04
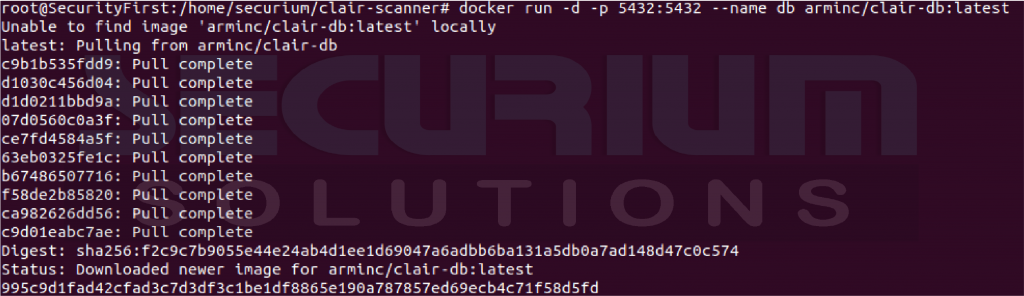
Now, we will run the docker image of the Clair scanning tool that will listen at local port number 5432. To run the docker image of Clair tool, use the following command:
# docker run -d -p 5432:5432 –name db arminc/clair-db:latest
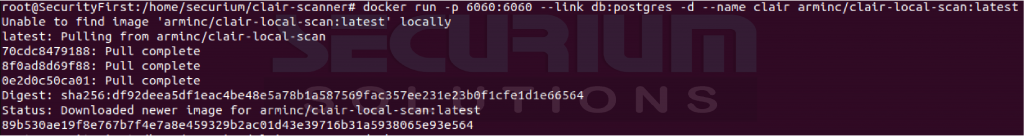
After running the docker image of Clair tool, we have to also run docker image of postgres database to link Clair scanning tool using following command:
# docker run -p 6060:6060 –link db:postgres -d –name clair arminc/clair-local-scan:latest
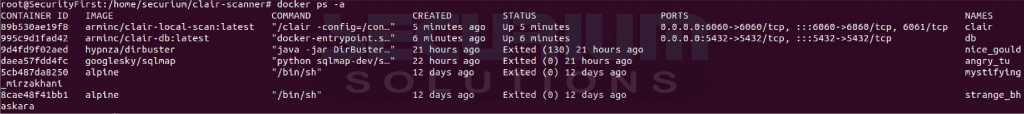
We can also check whether the docker image of Clair and postgress database is there in container or not with the help of following command:
# docker images

# docker ps -a
Now, it’s time to use the Clair scanner to scan the vulnerability of a docker image or docker container using the following command;
# ./clair-scanner –ip 172.17.0.1 -r report.json ubuntu:16.04

Here, 172.17.0.1 is a docker IP and Ubuntu is a docker Image.
From the above scanning report, we can see that we got 0 unapproved vulnerabilities in docker image of Ubuntu:16.04.
Author
Hard Dudhia
Cyber Security Intern